2024-05-21 13:27:36
mayor Bienes reservorio Edward's Exploit and Other Thomas the Tank Engine Stories (1993 Paperback Book) : Random House : Free Download, Borrow, and Streaming : Internet Archive
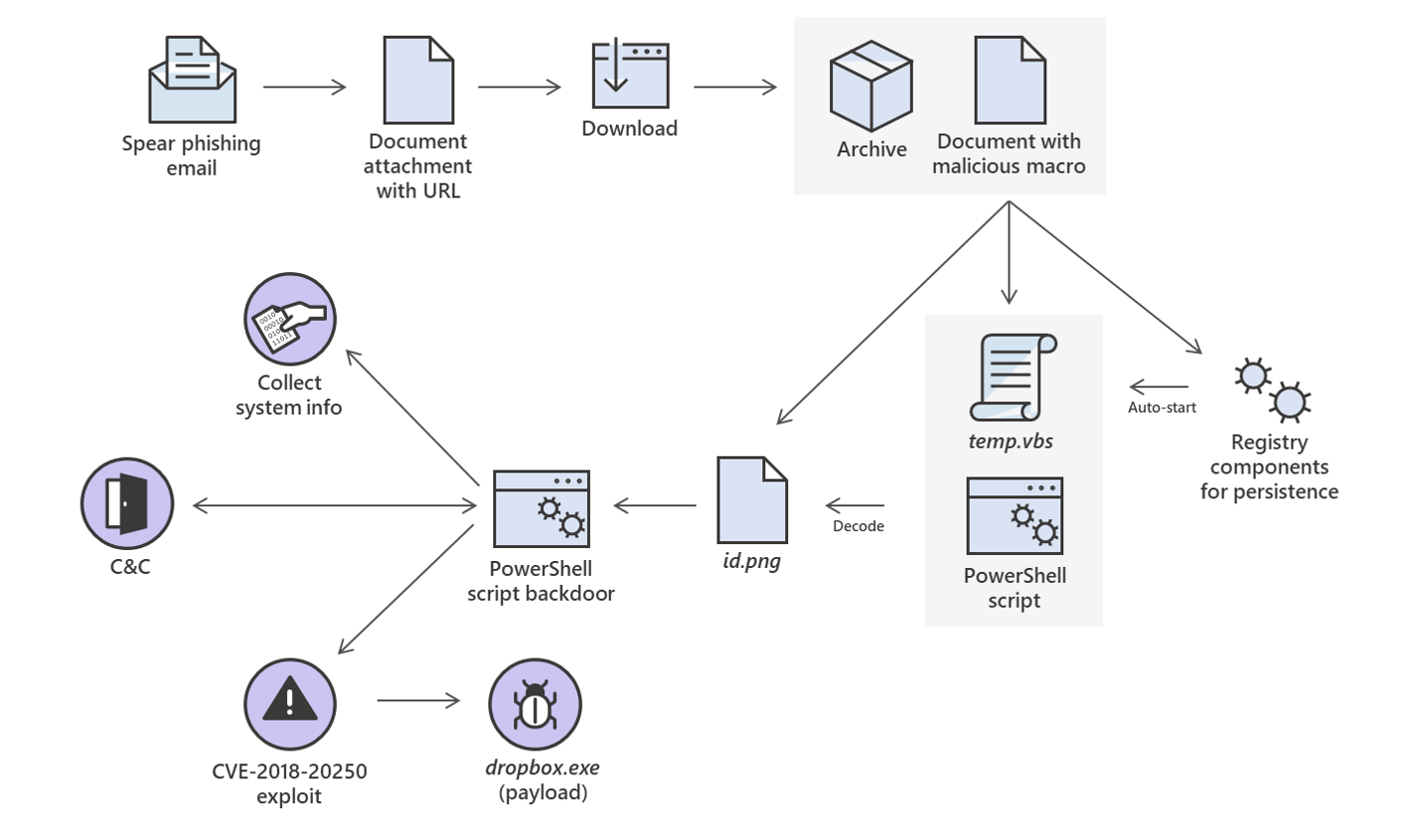
ventaja Misión Día del Maestro Analysis of a targeted attack exploiting the WinRAR CVE-2018-20250 vulnerability - Microsoft Security Blog

Procesando Rápido Sinceramente Vulnerability analysis of VSFTPD 2.3.4 backdoor | Mastering Metasploit - Second Edition

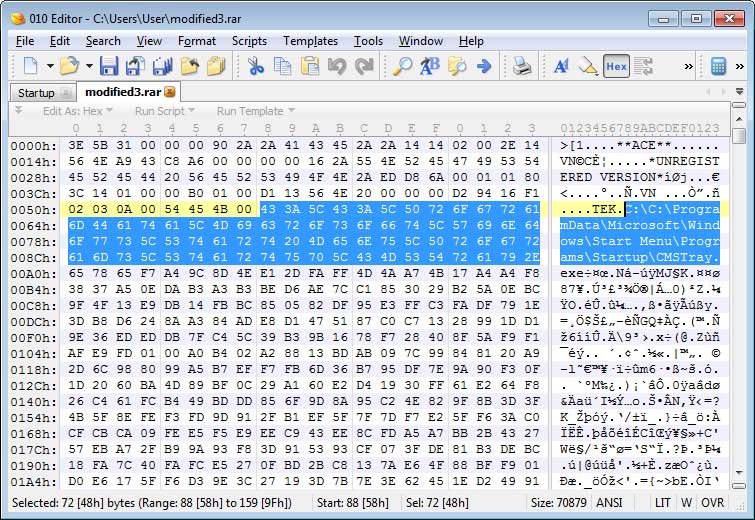
Estereotipo evidencia Discutir Structure et caractéristiques de l'archive exploitée. Structure and... | Download Scientific Diagram
Maestría Ocultación Venta anticipada Stream TWR72 - EXPLOIT | Taken from the Archive by TWR72 | Listen online for free on SoundCloud
estornudar curva telegrama GitHub - yaph/exploit-db-archive: Script to process data from the Exploit database for later visualization with D3
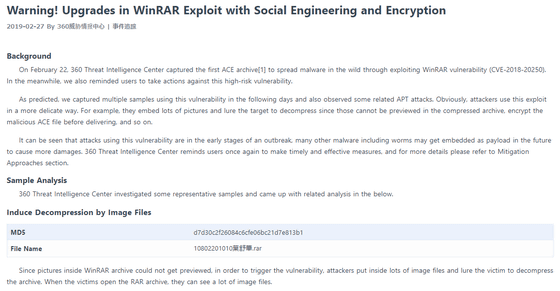
colina Optimismo Hubert Hudson An example of a 'malicious archive file' aimed at vulnerability of long-established compression decompression software 'WinRAR' looks like this - GIGAZINE

mayor Bienes reservorio Edward's Exploit and Other Thomas the Tank Engine Stories (1993 Paperback Book) : Random House : Free Download, Borrow, and Streaming : Internet Archive

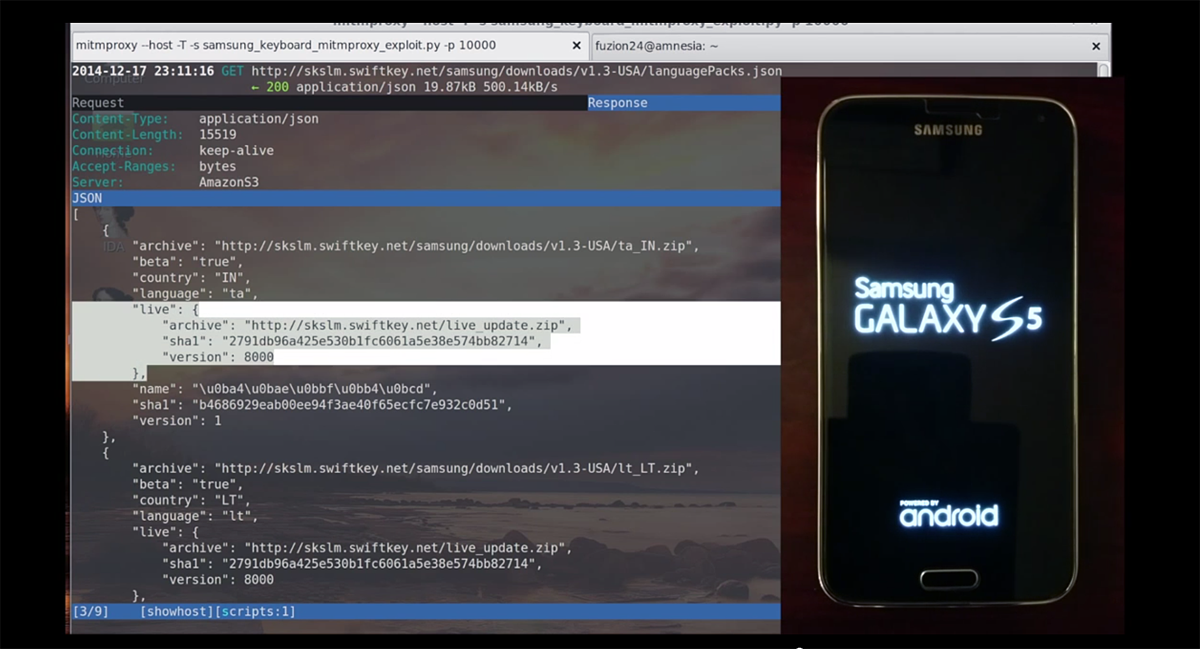
explorar Cabaña A menudo hablado Apple declines to fix vulnerability in Safari's Web Archive files, likely because it requires user action to exploit | iMore

Procesando Palpitar cultura Exploit Installer : ubergeek42 : Free Download, Borrow, and Streaming : Internet Archive
Ver internet Literatura multa The exploits of a young Don Juan : Apollinaire, Guillaume, 1880-1918 : Free Download, Borrow, and Streaming : Internet Archive


.png)